CISSP – Domain 2 Asset Security – 2020

CISSP – Domain 2 Asset Security – 2020 Free Tutorial Download
What you’ll learn
-
Deep understanding of the CISSP Domain 2 – Asset Security.
-
Get ready for taking the (ISC)² Certified Information Systems Security Professional (CISSP) examination.
-
Understand the importance of data classification and the implication that it has on the following steps of data management.
-
Distinguish between Personally Identifying Information (PII) and Protected Health Information (PHI).
-
Handle sensitive data, from labeling to destruction.
-
Be able to make the distinction between the different data roles and understand their scope of responsibilities.
-
Discern the seven Safe Harbor principles.
-
Get familiar with security controls baselines and standards.
Requirements
-
Be inclined to learn more about Asset Security.
-
Wanting to successfully prepare for the (ISC)² CISSP examination.
Description
Have you heard that the CISSP is the hottest cybersecurity certification?
Are you looking for the most detailed course on CISSP Domain 2 – Asset Security?
Are you interested in cyber security?
–> If the answer is YES, this course is for YOU.
Top three reasons to TAKE THIS COURSE right now!
- CISSP examination: This course will prepare you for the CISSP – Certified Information Systems Security Professional (CISSP) Certification Exam.
- Taught by a certified cyber professional: On top of the theory, I will share with you my insightful experience and illustrate it with concrete real-life examples.
- Next career step: This course will enable you to reach your next career step, to get an appealing cyber profile and set your learning journey into motion.
Overview
On a high-level, the course has three sections:
- Classifying and Labeling Data
- Identifying Data Roles
- Protecting Privacy
What’s in it for me, in detail?
The course is divided into three sections, subdivided into topics as following:
I. Classifying and Labeling Data
- Drafting Sensitive Data
- Data Classification
- Defining Security Requirements
- Three Different Data States
- Managing Sensitive Data
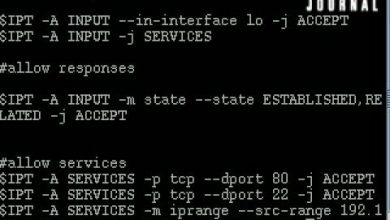
- Protecting with Cryptography
II. Identifying Data Roles
- The Six Data Roles
III. Protecting Privacy
- Basics to Protect The Privacy
Related information security certifications:
This CISSP course is perfectly designed for the preparation of IT Security certifications, ethical hacking penetration testing and for the following cyber security certifications:
- CISM Certified Information Security Manager certification from ISACA,
- CRISC Certified in Risk and Information Systems Controls certification from ISACA
- CCSP Certified Cloud Security Professional certification from (ISC)²
- CISSP concentrations: CISSP ISSAP, CISSP ISSEP, CISSP ISSMP
- CSSK Cloud Security certification from CSA
- CompTIA Security+ certification
In addition, you will also get:
✔ Unlimited Access to the course and all course updates.
✔ High quality support in the Q&A section.
✔ A Udemy “Certificate of Completion” for download (CPE/CEUs).
✔ BONUS: 10 CISSP practice questions for Domain 2.
What’s next? Hit the “Buy Now” or “Add to cart” button to start your CISSP course today !
See you in class !
Who this course is for:
- Juniors in cyber security willing to learn more about data classification, data roles, and privacy protection.
- Cyber experts that want to pass the CISSP examination.
- Anyone that wants to prepare the CISSP Domain 2 – Asset Security.
- Students preparing for the (ISC)² CISSP Certification Exam
Download CISSP – Domain 2 Asset Security – 2020 Free
https://beaconschool-my.sharepoint.com/:u:/g/personal/zcamacho_beaconschool_org/EeDpCDYffilKuW5iyF1aKxUB66IjFvlnMBH7oGBd9IHHRQ
https://bayfiles.com/B3Kev1T0o2
https://drive.google.com/file/d/1rqTuqWgotbWurOjQwUaXL68JkPep3dQB/view?usp=sharing
https://drive.google.com/file/d/13bzAsL7wdmtKF0LAhcYMSXRzQ9JmzVqp/view?usp=sharing
https://uptobox.com/eynz3fqg7q2x